SOC 2 Type I
Readiness & Preparation
Point-in-time validation of your control design (the essential first step toward formal SOC 2 certification).
Overview
A SOC 2 Type I report provides a "point-in-time" validation that your security controls are designed correctly. It is the essential first step for organizations that do not yet have a formal SOC 2 report and need to establish immediate credibility with prospects or enterprise partners. We formally define your audit scope, remediate gaps in your current security posture, and finalize the professional policies and procedures required to satisfy external auditors.
I have personally completed multiple SOC 2 engagements and seen organizations through to issued reports. This is not a framework I learned from a textbook.
I've worked with organizations that were confident their controls were solid, right up until an auditor started asking questions. The controls existed, but they weren't documented, weren't consistently executed, and weren't mapped to the criteria the auditor needed to see. The audit didn't fail because the company was insecure. It failed because they weren't audit-ready.
Scope Definition & Control Mapping
We identify all in-scope systems and map your organizational requirements to SOC 2 Common Criteria (CC1–CC9), giving you a clear, auditor-ready picture of what's covered and why.
Gap Remediation
We identify weaknesses in your current control design and work with your team to close them (before the auditor does). No surprises, no scrambling at the last minute.
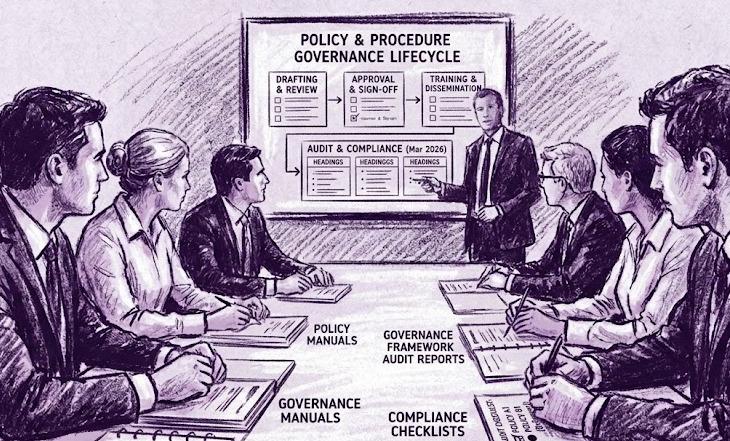
Policy & Documentation Finalization
We develop and finalize all required policies and procedures, draft the system description, and prepare the management assertion (in plain language your team can actually use).
Auditor Support
We support your external auditor through walkthroughs and inquiries, acting as the liaison between your team and the auditor to keep the engagement on track and on schedule.
Ideal for organizations that have designed their security controls but have not yet undergone a formal audit period. A Type I report establishes immediate credibility with enterprise buyers and partners (without waiting a full year for Type II coverage).
What You Can Expect
- SOC 2 scope and system description formally defined and approved
- All required policies and procedures finalized for audit
- Controls accurately mapped to CC1–CC9
- Gap identification and remediation before auditor engagement
- Full support through auditor walkthroughs, inquiries, and report issuance
Engagement Fee
SOC 2 Type I Readiness & Preparation
- Control design and documentation aligned to SOC 2 Common Criteria
- Evidence centralization and audit-ready state preparation
- External auditor relationship management through report issuance
Related Engagements
Once your Type I report is in hand, the natural next step is demonstrating that your controls operate effectively over time (not just that they're designed correctly).
- SOC 2 Type II (12-Month) Operating Effectiveness (the standard path for ongoing enterprise trust)
- SOC 2 Type II (3-Month) Accelerated Coverage (for urgent deadlines and bridge letter requests)
- SOC 2 Rescue (if a current engagement has stalled and needs to be taken over)
Who This Is For
- SaaS companies, technology vendors, and service providers responding to their first enterprise customer security questionnaire that requires a SOC 2 report
- Organizations with security controls in place that have never been formally audited or validated by an independent third party
- Companies that need to establish SOC 2 credibility quickly without waiting a full year for a Type II audit period
- Startups preparing for Series A or enterprise sales cycles where SOC 2 is a required due diligence item
- Organizations that previously attempted a SOC 2 engagement and stalled before reaching report issuance
Common Questions
What is the difference between SOC 2 Type I and Type II?
A SOC 2 Type I report validates that your security controls are suitably designed at a single point in time. A Type II report validates that those controls operated effectively over a defined audit period (typically 6 to 12 months). Type I is faster to obtain and establishes immediate credibility, but most enterprise customers and sophisticated buyers will eventually require Type II because it demonstrates sustained operational discipline, not just a well-designed program. Type I is the right starting point when controls are newly implemented or when a rapid assessment is needed to unblock a deal or sales cycle.
How long does a SOC 2 Type I engagement take?
A Type I engagement typically runs 6 to 10 weeks from kickoff to report issuance, depending on the current state of your controls and documentation, how quickly gaps can be remediated, and your external auditor's availability. Organizations with well-documented, operating controls can move faster. Organizations starting from scratch on policies and procedures should expect the longer end of the range. The timeline is set at engagement start so there are no surprises.
Do I need SOC 2 Type I before I can get Type II?
Not always. If your controls are already designed, documented, and operating, you can begin a Type II audit period without a Type I first. However, Type I serves an important role for organizations that have not yet had their controls reviewed by a third party: it validates the design before the operating period begins, giving you confidence that the controls you're executing for 12 months are the right ones. Skipping Type I and discovering a design gap mid-Type II is far more disruptive than catching it upfront.