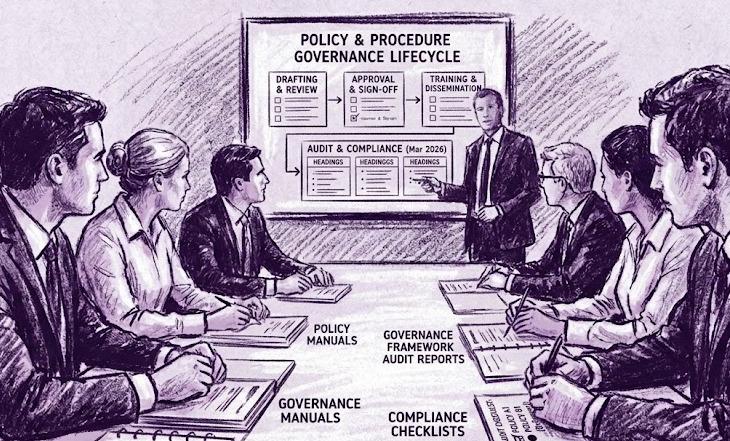
Policy & Procedure
Development and Auditing
Building the governance foundation your organization needs to operate securely and consistently.
Overview
Strong policies and procedures are the backbone of a mature cybersecurity program. Without them, even the best tools and talent operate without direction (leaving your organization exposed to risk, non-compliance, and operational inconsistency).
The policy existed. It lived in a folder on a shared drive. When the auditor asked whether employees had reviewed it, no one could say for certain. When they asked whether it had been updated in the last two years, the answer was no. Policies that no one reads aren't policies. They're a false sense of coverage.
Policy Development
We work with your leadership and IT teams to develop clear, enforceable policies covering information security, acceptable use, access control, incident response, and more (tailored to your industry and regulatory requirements).
Procedure Documentation
Policies without procedures are aspirations. We document the step-by-step processes your team needs to consistently execute on your security requirements, from onboarding to offboarding and everything in between.
Policy Auditing
We review your existing policies and procedures against current best practices, regulatory frameworks, and your actual operations (identifying gaps, outdated language, and areas of risk before auditors or incidents do).
Think compliance frameworks don't apply to you? Cyber liability insurance applications require the same solid policies and procedures (and insurers are looking closely at whether yours hold up).
What You Can Expect
- A comprehensive review of your current documentation landscape
- Gap analysis against applicable frameworks (NIST, ISO 27001, SOC 2, etc.)
- Newly developed or revised policies in plain, actionable language
- Documented procedures aligned to your real-world workflows
- An executive summary suitable for board or leadership reporting
Mid-audit and things have stalled? If a SOC 2 engagement with another consultant has gone quiet, SOC 2 Rescue is a flat-fee engagement to step in, assess the situation, and get things moving again.
Who This Is For
- Organizations preparing for their first formal compliance audit (SOC 2, ISO 27001, HIPAA, PCI DSS)
- Businesses that failed an audit or received findings related to missing or outdated documentation
- Companies applying for or renewing cyber liability insurance (insurers increasingly require documented security policies)
- IT and security teams building a governance framework aligned to NIST CSF or ISO 27001
- Organizations that have grown quickly and now operate without consistent, enforceable procedures
Common Questions
What cybersecurity policies does every organization need?
At minimum, organizations need an information security policy, acceptable use policy, access control policy, incident response policy, and data classification and handling policy. Regulated industries (healthcare, finance, payment processing) require additional policies tied to specific frameworks. We assess your current documentation against your industry, size, and applicable compliance requirements to identify exactly what is missing or needs to be updated.
How often should security policies be reviewed and updated?
Annual review is best practice and a requirement of most compliance frameworks including SOC 2, ISO 27001, and HIPAA. Policies should also be updated when there is a significant change to your environment, a new regulatory requirement, or a security incident that exposed a gap. Most organizations fall behind on this until an audit or an incident makes the problem visible.
What is a policy gap analysis, and what does it produce?
A policy gap analysis compares your existing documentation against a target framework (NIST CSF, ISO 27001, SOC 2, or your specific regulatory requirements) and identifies what is missing, outdated, or inconsistent with how you actually operate. The output is a prioritized gap report with a work plan for developing or updating each affected document.